Environment
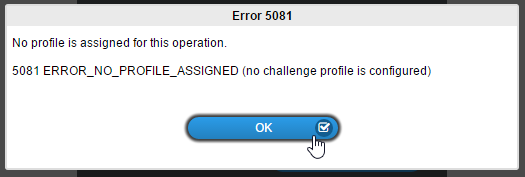
Situation
Resolution
First, make sure
your configuration is unlocked. To do this, go to your SSPRConfiguration.xml
and set configIsEditable to True. See TID 7014954 - SSPR Configuration Manager is not available for details on this.
Once you've done this, go into the Configuration Editor. Use the following steps to "refresh" the policies you've set.
- Go to Policies > Challenge Policies > Select your Policy profile ("default" is the default policy, if that is what you are using).
- Take note of your current LDAP filter settings. You'll need to put them back in later.
- Click the red "x" to remove the LDAP filter.
- Repeat steps 2 & 3 for Policies > Password Policies > Your Policy Profile.
- Save your configuration. This will restart the SSPR service.
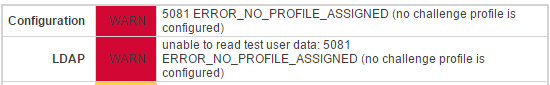
- Logout of SSPR - You should still see the "Warning" on the right, showing you don't have a profile set.
- Go back into the Configuration Editor.
- For the Challenge Policy, add the LDAP filter back in.
- Do the same for the Password Policy.
- Save your settings again.
At this point, the
error should be corrected. The policies are now being correctly recognized. If
they are not, then make sure you entered your LDAP Filter search parameters
correctly. Click "View Matches" (back on the Policy profile's
settings) to make sure that it's finding users as it should.
Remember to lock your configuration again, and switch configIsEditable to False instead of True.
Other Possible Resolutions.
I. This error has been seen when the user does have a matching password policy, or if there is not a default password policy for SSPR. If the above suggestions do not work and you do not have a default password policy in SSPR, try configuring a new password policy called default with all default settings and see if the error goes away then.
II. The error has been seen if you have an invalid search filter specified in the Password Policy Profile Match.
- To fix the issue, you need to unlock the configuration through the appliance admin console (https://serveripaddress:9443), under Administrative commands, Unlock Configuration.
- Then go into configuration Editor and change the Password Policy Profile Match to objectclass=* (default) https://IPAddressOfServer/sspr/private/config/ConfigEditor
- Under Policies ⇨ Password Policies ⇨ default -> Password Policy Profile Match, under the LDAP Search Filter change objectclass=cn to objectclass=*, then save the configuration and test.
- Once it is verified working go back into the Appliance admin console or Configuration Manager and lock the configuration.