Summary
Error
Older versions of Server Automation (SA) will silently accept corrupted copies of the wsusscn2.cab patch database. This database will then be distributed to any managed Windows server during its next software inventory. A corrupted wsusscn2.cab on a managed Windows server will cause this software inventory to always fail. It will also cause all Windows patch remediation activities to fail.
Cause
Sometimes corrupted copies of wsusscn2.cab will be present on some nodes of Microsoft's web server cloud. Whether or not you end up downloading one of these corrupted copies will then depend on how your server resolves the hostname "download.windowsupdate.com".
Fix
Defensive logic was added via the following hotfix rollup line item that causes HPSA to reject corrupted wsusscn2.cab files:
QCCR1D233320 - SA silently accepts corrupted wsusscn2.cab files (note: the QCCR ID will vary from SA version to SA version)
The best workaround is to install a hotfix rollup that contains the above fix.
You can check to see if your currently installed hotfix rollup contains this fix by executing the following command on one of your HPSA slices and looking for results that match the description above.
# find /opt/opsware/hotfix/ -iname readme.txt | xargs grep wsusscn2.cab
Whether or not you have this fix in place, it is a good idea to manually download the wsusscn2.cab to your workstation, so that you can verify that it is valid before uploading it into HPSA manually via the java client.
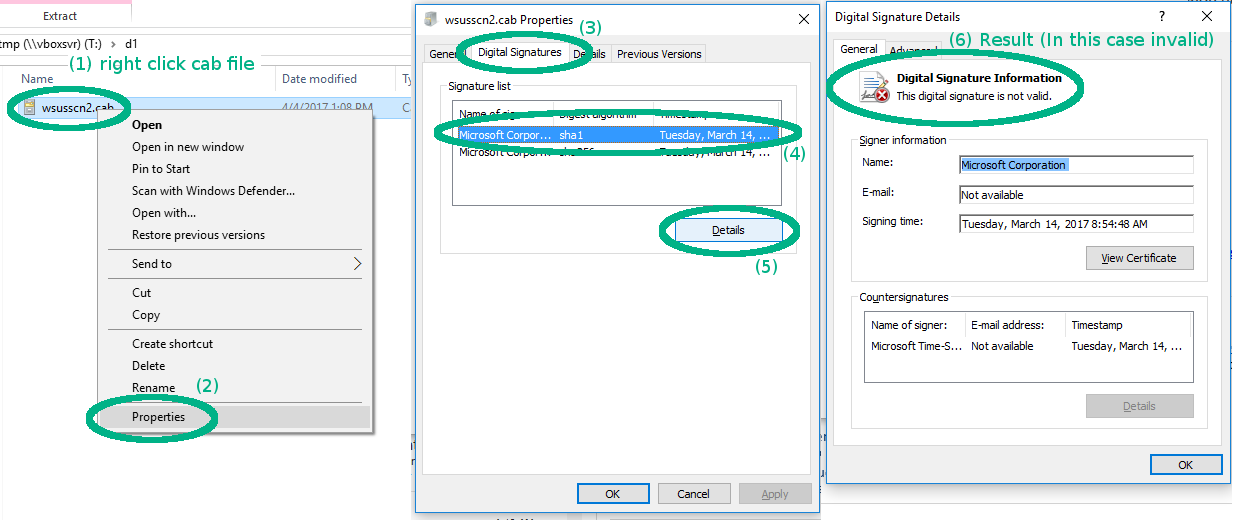
Once you download the cab file, you can manually verify the embedded signature by performing the following steps:
- right-click the cab file
- select "Properties"
- select "Digital Signatures" tab
- select one of the listed signatures.
- click the [Details] button
- The result of will be displayed at the top.