Environment
GWAVA (Secure Messaging Gateway) 7
GroupWise Mobility Service 18.2
GroupWise 18.2
Situation
You would like to have a control over a contents of emails being sent from mobile devices via GMS.
Resolution
This article describes a way how to make GMS 18.2 working together with Secure Messaging Gateway 7 (SMG 7).
First start with the SMG 7 host.
Login to webadmin tool of SG7 host and choose System Administration from options provided.
Under Module Management, there is a section Interfaces with 3rd Party Application Manager.
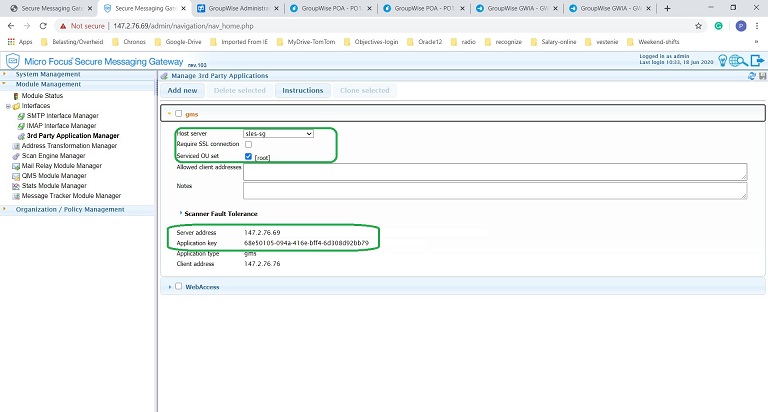
Click on Add new. Name it gms, for instance.
Once you expand it, in the Host server choose from the drop down menu your SMG server. Activate Service OU set [root] option. Once you save it and then return back, you will see server address and application key being auto-populated. Those values we will need later in GMS part.
In next step go into Organization/Policy Management and click on Policy Management.
Here click on Add New since there is no wizard for it. Name it for simplicity gms.
Once it is created and changes saved, you can expand and configure next settings.
First, make sure it is enabled.
GMS has no message direction, so leave it unchecked.
Activate "Limit by interface type" and in Matched interface types type gms. Note, you could choose whatever other names for the policy or interface, but here a string "gms" is a must.
Choose also Limit interface option and select from the list the one you just created, i.e gms in this example.
Save changes.
After that you can find under Policy scan configuration new entry gms and in workbench you can start configuring what you want to scan and protect.
After you are ready with SMG section, move to a GMS server.
Since SMG checks user devices activity, the changes we must do are within the mobility connector.
Go into /etc/datasync/configengine/engines/default/pipelines/pipeline1/connectors/mobility directory.
Make first a backup of existing connector.xml file prior editing it in a text editor.
Find the section <custom> and go to the closing tag </custom>. Add above that line next lines, example:
<securegatewayEnable>1</securegatewayEnable>
<securegatewayHost>mysg7.com</securegatewayHost>
<securegatewayPort>443</securegatewayPort>
<securegatewaySecure>1</securegatewaySecure>
<securegatewayAppkey>68e50105-094a-416e-bff4-6d308d92bb79</securegatewayAppkey>
<securegatewayHost>mysg7.com</securegatewayHost>
<securegatewayPort>443</securegatewayPort>
<securegatewaySecure>1</securegatewaySecure>
<securegatewayAppkey>68e50105-094a-416e-bff4-6d308d92bb79</securegatewayAppkey>
In your case in Host tag, type fully distinguished name of your SMG host or its IP address.
In Appkey tag, return to you Interfaces -> 3rd party -> gms and expand it. You will find there the Application Key string that comes into this tag.
After that save changes and restart gms services. Since now, your GMS server and SMG host are linked and the SMG would scan emails sent between GW and GMS.
If the SMG is your first initial install and you use self-signed certificates, then you might face problems with sending emails from a mobile device although a test mail shall not violate any filters you configured in the benchmark.
If you check GMS logs in DEBUG, the mobility-agent.log, then you might see a line like example bellow:
2020-06-18 11:05:52.858 ERROR [Device_Thread-35] [gwavascan:229] [userID:] [eventID:] [objectID:] [] ConnectionError: HTTPSConnectionPool(host='147.2.76.69', port=443): Max retries exceeded with url: /api/1/mimescan.xml?appkey=68e50105-094a-416e-bff4-6d308d92bb79 (Caused by SSLError(SSLError("bad handshake: Error([('SSL routines', 'tls_process_server_certificate', 'certificate verify failed')],)",),)); Url: https://147.2.76.69:443/api/1/mimescan.xml?appkey=68e50105-094a-416e-bff4-6d308d92bb79
That show the GMS server could not make a secure connection to your SMG host, in this line it is "147.2.76.69".
For testing you can workaround it by setting the connector.xml not to use secure, but insecure connection, i.e.
<securegatewayEnable>1</securegatewayEnable>
<securegatewayHost>mysg7.com</securegatewayHost>
<securegatewayPort>80</securegatewayPort>
<securegatewaySecure>0</securegatewaySecure>
<securegatewayAppkey>68e50105-094a-416e-bff4-6d308d92bb79</securegatewayAppkey>
<securegatewayHost>mysg7.com</securegatewayHost>
<securegatewayPort>80</securegatewayPort>
<securegatewaySecure>0</securegatewaySecure>
<securegatewayAppkey>68e50105-094a-416e-bff4-6d308d92bb79</securegatewayAppkey>
Save then changes and restart GMS services. Now, if you compose new email on a mobile device, that would hit one of filters that result in a message blocking, you will not be able to send email successfully. You will receive right after you send such bad test email a new message that your email was no possible to send, it was blocked by Secure Gateway.